Securing your property involves more than just locking the doors. In fact, British companies lose an estimated £1 billion each year due to preventable security breaches. Understanding where your vulnerabilities lie and choosing the right access control systems matters for both peace of mind and real safety. By following a step-by-step approach, you can build strong protection, avoid common pitfalls, and create a safer environment for everyone on site.
Quick Summary
| Key Insight | Explanation |
|---|---|
| 1. Conduct a thorough site survey | Map all access points and assess their security to identify vulnerabilities and necessary interventions early on. |
| 2. Choose access control systems wisely | Select systems and components that align with your security needs and can integrate with existing infrastructure for better protection. |
| 3. Prepare wiring infrastructure carefully | Ensure optimal routing of wiring while adhering to electrical standards, allowing for future expansions without complete rewiring. |
| 4. Install hardware with precision | Mount access control components correctly to ensure functionality and user comfort for effective security performance. |
| 5. Document setup and train staff effectively | Create detailed documentation and structured training for staff to ensure proper system usage and ongoing security awareness. |
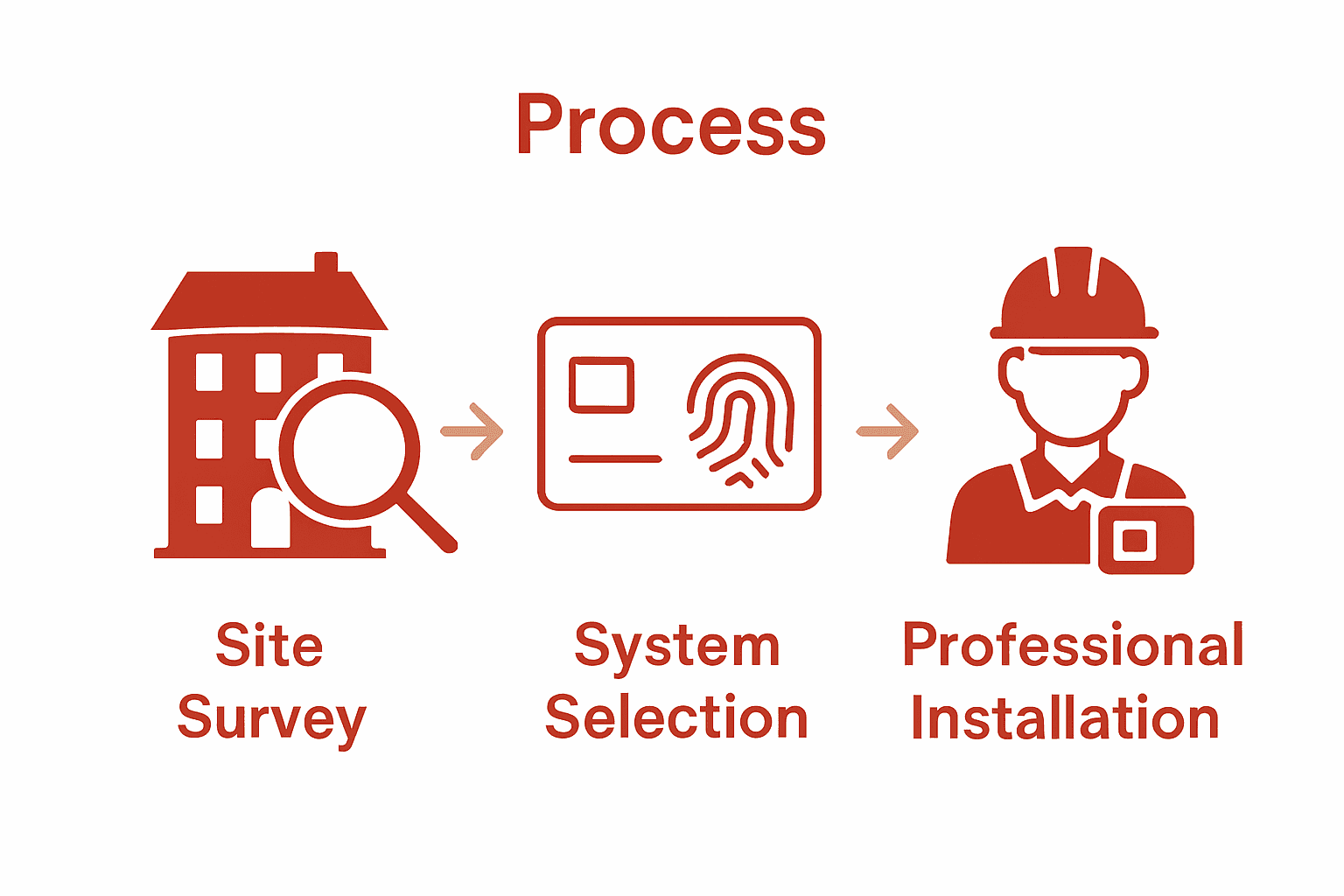
Stage 1: Assess security needs and plan access points
Securing your property starts with a strategic and methodical approach to understanding your unique security landscape. According to the National Protective Security Authority, integrating security considerations early in the planning process is crucial for minimising vulnerabilities and creating robust protection.
Begin by conducting a comprehensive site survey that maps out all potential access points and evaluates their current security status. This involves walking through your property and identifying every entrance including main doors, side gates, loading bays, emergency exits, and even less obvious entry routes. Pay close attention to high traffic areas, zones with sensitive equipment or valuable assets, and locations that might be vulnerable to unauthorized access.
Your security assessment should categorise access points based on risk levels. Low risk areas might include public reception spaces, while high risk zones could include server rooms, cash handling areas, or storage of confidential documents. For each identified access point, determine the appropriate level of security required such as keycard access, biometric verification, or physical security personnel. UK Government Security Group recommends embedding security measures throughout your development process to create a holistic protection strategy.
Pro tip: Document everything meticulously. Create a detailed floor plan with annotated access points, potential risks, and recommended security interventions. This visual map will be invaluable when designing and implementing your final access control system.
The next stage involves translating these insights into a precise access control strategy that matches your specific security requirements.
Stage 2: Choose appropriate access control systems and components
Selecting the right access control system is a critical decision that will define your property’s security infrastructure. According to the National Protective Security Authority, choosing components that align precisely with your security requirements and operational needs is fundamental to creating an effective protection strategy.
Start by evaluating different system types such as keycard, biometric, proximity card, and smart token systems. Each technology offers unique advantages depending on your specific environment. Keycard systems work well in traditional office settings, while biometric solutions like fingerprint or facial recognition provide higher security for sensitive areas. NPSA’s guidance on perimeters and checkpoints recommends considering threat levels and site specific security needs when making your selection.
Pay close attention to system components including readers, controllers, and credentials. Look for scalable solutions that can integrate seamlessly with your existing infrastructure and allow for future expansion. Compatibility with other security systems like CCTV and alarm networks will provide a more comprehensive security approach. [Learn more about integrating access control systems seamlessly into your workplace.
Pro tip: Always consider both technological capabilities and user experience. A highly secure system that frustrates employees can lead to workarounds that compromise your overall security strategy.
With your components selected, you are now ready to move forward to the installation and implementation phase.
Stage 3: Prepare site and install wiring infrastructure
Preparing your site for access control installation requires meticulous planning and a strategic approach to infrastructure development. UK Government Security Group recommends carefully mapping out your architectural requirements before beginning any physical installation work.
Start by conducting a thorough electrical and network infrastructure assessment. Identify optimal routing paths for your access control wiring that minimise exposure and potential interference. This typically involves mapping out concealed conduits along walls, ceiling spaces, and utility corridors where cables can be safely and discreetly installed. Pay special attention to power sources ensuring they can support your access control system’s electrical requirements. Consider installing dedicated electrical circuits for critical security infrastructure to prevent potential power disruptions.
When running cable infrastructure, prioritise using high quality CAT6 or CAT7 ethernet cables for network connectivity and separate power lines for each access control component. This approach ensures robust signal transmission and reduces electromagnetic interference.
 Implement proper cable management techniques such as using cable trays, conduits, and precise labelling to maintain a clean and organised installation. Ensure all wiring meets current British electrical standards and building regulations.
Implement proper cable management techniques such as using cable trays, conduits, and precise labelling to maintain a clean and organised installation. Ensure all wiring meets current British electrical standards and building regulations.
Pro tip: Always include extra cable length and additional conduit space during initial installation. This foresight allows for future system expansions or technological upgrades without requiring complete rewiring.
With your wiring infrastructure prepared, you are now ready to move forward to mounting access control hardware and configuring system components.
Stage 4: Fit and configure access control hardware
Installing access control hardware is a precise process that requires careful attention to detail and strategic placement. National Protective Security Authority guidelines emphasise the critical importance of proper hardware installation to ensure optimal security performance.
Begin by mounting access control readers at standard height approximately 1.2 metres from the ground. This ensures comfortable interaction for most users while maintaining a clear line of sight. Place electronic locks, strike plates, and magnetic contacts with precision. For door access control systems in London and Essex businesses, positioning is crucial for seamless functionality. Pay special attention to door frame alignment ensuring that electronic components interact smoothly without mechanical strain. NPSA’s recommendations on building entry points suggest configuring hardware to balance security requirements with practical user experience.
Carefully connect each hardware component to your central control unit. This involves meticulously routing cables through pre installed conduits, ensuring secure connections and minimising potential signal interference. Programme individual access levels into the system, defining precise permissions for different user groups.
Consider creating graduated access hierarchies that reflect your organisation’s specific security needs.
Pro tip: Always conduct thorough testing after installation. Verify each reader, lock, and credential works precisely as intended before considering the configuration complete.
With hardware successfully fitted and configured, you are now prepared to programme and fine tune your access control system.
Stage 5: Test system functionality and user access
Testing your access control system is a critical phase that validates the entire installation process. UK Government Security Group emphasises the crucial importance of systematically verifying security controls to ensure comprehensive protection.
Begin with a comprehensive functionality test that covers every aspect of your access control system. This involves methodically checking each reader, credential, and access point to confirm they respond exactly as programmed. NPSA’s guidance on building and area search recommends creating a structured testing protocol that simulates various access scenarios. Start by testing individual user credentials across different access levels ensuring that authorised personnel can enter designated areas while unauthorised access is consistently blocked.
Conduct a series of deliberate test scenarios that challenge your system’s capabilities. This includes verifying emergency override protocols, testing credential responses under different conditions such as low battery or network interruption, and confirming that access logs accurately record all entry and exit events. Pay special attention to edge cases such as multiple simultaneous access attempts, credential expiration, and system response times.
Pro tip: Document every test result meticulously. Create a comprehensive testing log that captures each scenario, expected outcome, and actual system performance. This documentation will prove invaluable for future system maintenance and potential security audits.
With thorough testing complete, your access control system is now ready for full operational deployment.
Stage 6: Document system setup and provide staff training
National Protective Security Authority guidelines emphasise the critical importance of comprehensive documentation and staff training as fundamental elements of an effective security strategy. Creating a robust documentation system and training programme ensures that your access control investment delivers maximum protection and operational efficiency.
Begin by developing a detailed technical documentation package that includes comprehensive system diagrams, network architecture layouts, hardware specifications, and configuration details. This documentation should provide a complete blueprint of your access control infrastructure, enabling future maintenance and potential system expansions. Include precise instructions for credential management, emergency access protocols, and troubleshooting procedures. UK Government’s ‘Secure in the Knowledge’ guide recommends creating training materials that are clear, concise, and tailored to different staff roles and responsibility levels.
Design a structured training programme that covers system operation, security protocols, and potential threat scenarios. This should include practical demonstrations of credential usage, understanding access levels, reporting suspicious activities, and responding to potential security breaches. Develop different training modules for administrators, security personnel, and general staff members, ensuring each group receives role specific information. Schedule regular refresher sessions to keep staff updated on system changes and emerging security best practices.
Pro tip: Create a visual quick reference guide that staff can easily access, outlining key procedures such as reporting lost credentials, understanding access restrictions, and emergency contact information.
With documentation completed and staff training initiated, your access control system is now fully prepared for operational deployment.
Strengthen Your Property Security with Expert Access Control Installation
Securing your property effectively requires more than just understanding the steps in an installation guide. The challenges of selecting the right access control systems, preparing wiring infrastructure, and ensuring flawless hardware configuration are complex and demand professional expertise. From managing risk levels at multiple access points to implementing precise control hierarchies, many businesses and homeowners face the daunting task of balancing security with ease of use.
At 247 CCTV we specialise in delivering tailored access control solutions that address these critical pain points. Our experienced team helps you assess your unique security requirements, fits advanced door entry and access systems, and conducts rigorous testing to guarantee performance you can trust. Don’t leave your property’s safety to chance.
Take the stress out of protecting your premises by partnering with us today. Explore our range of access control installations and discover how seamless integration with CCTV and burglar alarms can create a comprehensive security shield. Visit 247 CCTV now to secure your property with confidence and professional care.
Frequently Asked Questions
What initial steps should I take to assess my property’s security needs for access control?
Start by conducting a comprehensive site survey to identify all potential access points and evaluate their current security status. Walk through your property, documenting each entrance and categorising them based on risk levels to determine the necessary security measures.
How do I choose the right access control system for my property?
Evaluate different system types such as keycard, biometric, and proximity card systems. Choose the system that best fits your specific environment and security requirements, ensuring it is scalable and integrates well with existing technologies.
What should I consider when preparing the site for access control installation?
Assess your electrical and network infrastructure to determine optimal pathways for wiring. Ensure adequate power sources are available and install high-quality cables while following relevant electrical standards.
How do I mount and configure access control hardware accurately?
Mount access control readers at a standard height of 1.2 metres to ensure effective usability. Carefully connect all components to the central control unit, programming individual access levels according to your specific security needs to maintain optimal functionality.
What testing procedures should I follow to ensure my access control system is functioning properly?
Conduct a comprehensive functionality test covering all aspects of the system, verifying every reader, credential, and access point. Document the results meticulously to ensure all permissions and security features work as expected before moving to full deployment.
How can I effectively train staff to use the access control system?
Design a structured training programme tailored to different roles, covering system operation and security protocols. Include practical demonstrations and regular refresher sessions to keep staff informed about updates and best practices.
Recommended
- Integrating Access Control Systems Seamlessly into Your Workplace – 247 CCTV Security Ltd
- Enhancing Business Security with Advanced Access Control Solutions – 247 CCTV Security Ltd
- Integrating Access Control Systems Seamlessly into Your Workplace – 247 CCTV Security Ltd
- Enhancing Business Security with Advanced Access Control Solutions – 247 CCTV Security Ltd










