Many business and property managers still rely on traditional locks, believing they provide adequate security. However, modern threats demand more sophisticated solutions. Access control systems offer audit trails, remote management, and scalable permissions that traditional keys simply cannot match. This guide explores proven methodologies and physical systems to help you select the most effective approach for your Essex or London property, balancing security, cost, and operational needs.
Key Takeaways
| Point | Details |
|---|---|
| RBAC widely used | Role based access control is the most widely used methodology in commercial properties, simplifying administration but prone to role explosion as organisations grow. |
| ABAC for granularity | Attribute based access control evaluates multiple factors such as user attributes, time and location before granting access, offering granular control for complex environments. |
| Hybrid RBAC ABAC | A practical approach combines RBAC baseline permissions with ABAC rules for sensitive areas to provide manageable roles alongside contextual security. |
| Traditional locks lack audit | Traditional lock systems are cheap and simple but offer no audit trails and make revocation difficult when personnel change. |
| Card access audits | Card based systems create audit trails showing who entered each door and when and access can be revoked through software. |
Understanding access control methodologies
Access control manages who enters specific areas and when, forming the foundation of modern property security. Unlike traditional locks that grant blanket access to anyone holding a key, access control methodologies enable precise permission management tailored to individual roles and circumstances.
Discretionary Access Control (DAC) allows resource owners to determine who accesses their areas. Whilst simple to implement, DAC creates security risks in commercial settings where multiple stakeholders need oversight. Mandatory Access Control (MAC) enforces strict, system-wide policies based on security classifications, making it suitable for government facilities but overly rigid for most business environments.
Role-Based Access Control (RBAC) assigns permissions according to job functions, making it the most widely used methodology in commercial properties. A facilities manager receives different access rights than a cleaner or contractor. RBAC streamlines administration when you have clearly defined roles. However, organisations often face role explosion as they grow, creating dozens of overlapping permissions that become difficult to manage. You might start with five roles and end up with thirty variations, each requiring separate maintenance.
Attribute-Based Access Control (ABAC) evaluates multiple factors including user attributes, resource characteristics, and environmental conditions before granting access. Rather than simply checking job title, ABAC considers time of day, location, and current security level. This granular approach suits complex environments like hospitals or multi-tenant office buildings where access needs vary by context. An employee might access the server room during business hours but not at weekends, regardless of their role.
Pro tip: Combine RBAC for baseline permissions with ABAC rules for sensitive areas. This hybrid approach provides manageable role structures whilst adding contextual security where it matters most.
The access control installation guide explains how these methodologies translate into practical systems. Consider your property’s complexity, user count, and security requirements when selecting an approach. Smaller properties often succeed with straightforward RBAC, whilst larger or multi-use facilities benefit from ABAC’s flexibility.
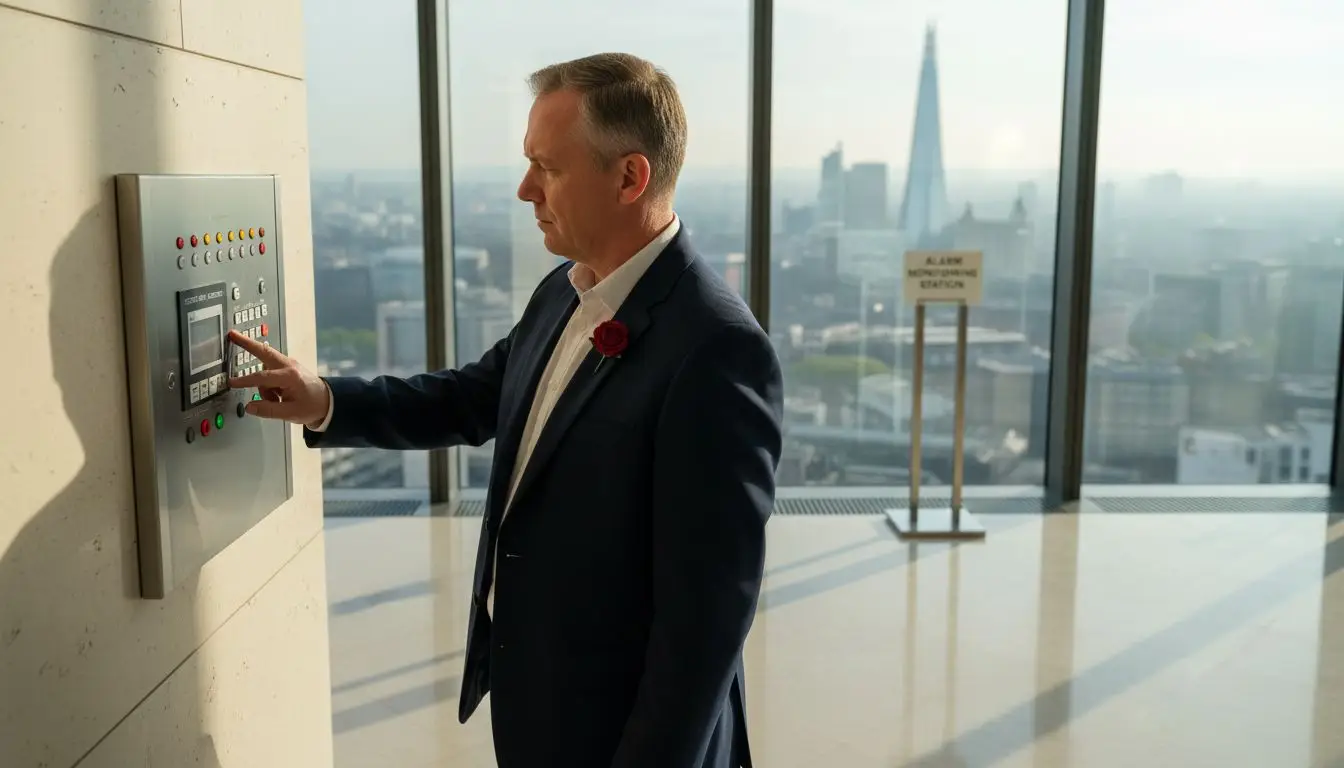
Physical access control systems: types and considerations
Physical systems implement the methodologies discussed above through tangible hardware and software. Each type offers distinct advantages and limitations that directly impact your security investment.
Traditional locks remain common due to low initial costs and simple operation. You purchase locks, distribute keys, and replacement requires only a locksmith visit. However, traditional systems lack audit capabilities and make access revocation impractical. When an employee leaves or loses a key, you face expensive rekeying across multiple doors. You cannot track who entered which areas or identify security breaches after incidents occur.
Card access systems use proximity cards or key fobs to grant entry through electronic readers. These scalable solutions create audit trails showing exactly who accessed each door and when. Revoking access requires only deactivating a card in software rather than changing physical locks. Card systems integrate well with time and attendance tracking, providing operational benefits beyond security. The main vulnerability involves card cloning and sharing. Employees sometimes lend cards to colleagues, undermining your security protocols. Lost cards create temporary risks until deactivated.
Biometric systems authenticate users through fingerprints, facial recognition, or iris scans. These methods provide the highest security level since biological characteristics cannot be shared or stolen like cards. Users appreciate not carrying additional credentials. However, biometric systems cost significantly more than card readers and may prove impractical for smaller properties. Some users have privacy concerns about biometric data storage. Environmental factors like dirt or glare can affect reader accuracy.

Cloud-based controllers enable remote management through web interfaces, allowing you to grant access, review logs, and receive alerts from anywhere. This flexibility suits property managers overseeing multiple sites or requiring after-hours administration. Cloud systems scale easily as you add doors or users. The trade-off involves cybersecurity risks from internet connectivity and dependence on service providers. On-premise controllers store data locally and operate independently of internet connections, providing direct control but limited remote access.
Pro tip: Layer your physical access control with video surveillance at entry points. When someone uses credentials to enter, corresponding footage creates visual verification that strengthens security investigations and deters credential sharing.
| System type | Security level | Cost | Scalability | Audit capability |
|---|---|---|---|---|
| Traditional locks | Low | Very low | Poor | None |
| Card systems | Medium | Moderate | Excellent | Full |
| Biometric | Very high | High | Good | Full |
| Cloud-based | Medium-high | Moderate | Excellent | Full |
| On-premise | Medium-high | High | Good | Full |
Explore door entry systems and review office door entry solutions to see how different physical systems apply to various property types.
Choosing the right access control method for your property
Selecting appropriate access control requires evaluating your specific security requirements, operational context, and budget constraints. Generic recommendations rarely suit individual properties effectively.
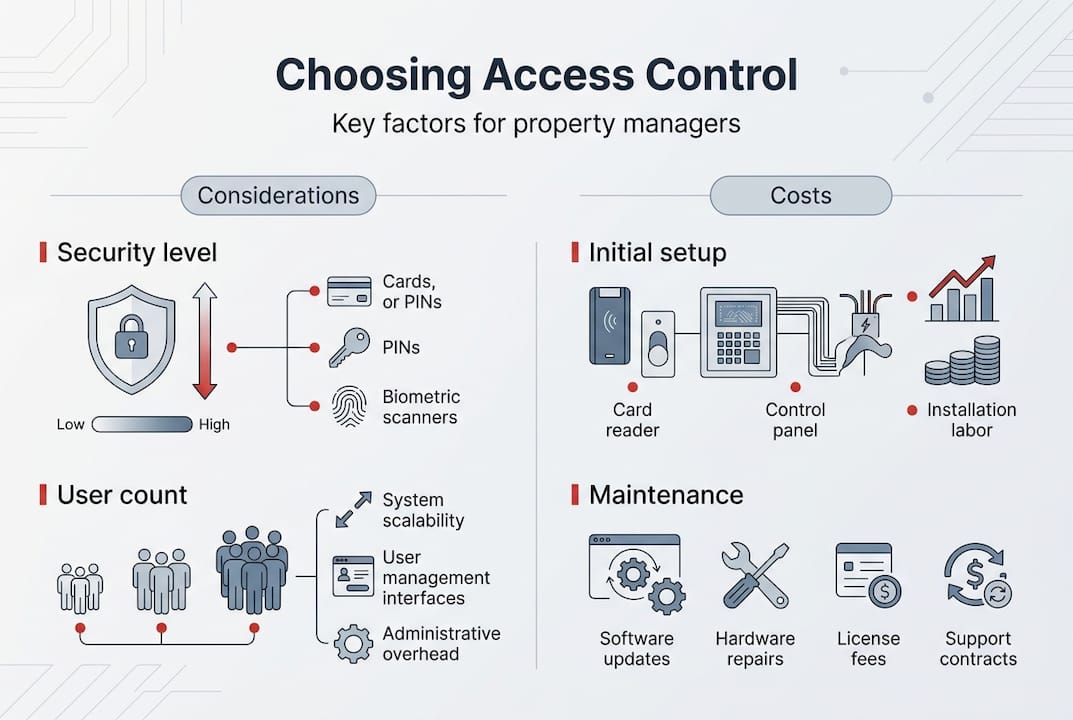
Security requirements vary dramatically between a small retail shop and a multi-tenant office building. Assess your risk profile honestly. What assets need protection? How severe would unauthorised access consequences be? Properties storing valuable inventory or sensitive data justify higher security investments than low-risk environments. Consider external threats like break-ins alongside internal risks from unauthorised employee access.
User count directly impacts system complexity and cost. Five employees might manage well with traditional locks, whilst fifty users create key management nightmares. RBAC systems handle growing user bases efficiently until role explosion occurs, typically around 100-200 users depending on organisational complexity. Larger properties or those anticipating growth should consider ABAC or hybrid approaches from the start.
Budget constraints extend beyond initial hardware costs. Factor in installation, ongoing maintenance, software licences, and eventual upgrades. Electronic systems require power backup provisions to maintain security during outages. Cloud services involve recurring subscription fees whilst on-premise systems need local IT support. Calculate total cost of ownership over five years rather than focusing solely on upfront expenses.
User convenience affects compliance and operational efficiency. Systems that frustrate legitimate users encourage workarounds like propped doors or shared credentials. Biometric readers offer seamless access but may slow entry during peak times if authentication takes several seconds per person. Card systems balance speed and security well for most commercial applications.
Selecting your access control system:
- Document all entry points requiring control and classify them by security sensitivity
- List user groups with their access needs and estimate growth over three years
- Define your security priorities including audit requirements and incident response needs
- Research systems meeting your technical requirements and request demonstrations
- Calculate total five-year costs including installation, maintenance, and upgrades
- Pilot your preferred system on high-traffic doors before full deployment
- Develop clear protocols for granting, reviewing, and revoking access permissions
- Train all users and administrators thoroughly on proper system operation
Pro tip: Review access permissions quarterly rather than waiting for annual audits. Outdated credentials from departed employees or changed roles create significant security vulnerabilities that regular reviews quickly identify.
The access control installation guide provides detailed implementation steps. Consider how access control integrates with workplace operations to ensure your chosen system enhances rather than hinders daily activities.
Maintaining and integrating access control for sustained security
Installing access control represents only the beginning of effective security management. Ongoing maintenance and strategic integration with other systems determine whether your investment delivers sustained protection.
Monitoring access logs reveals patterns that indicate security issues before breaches occur. Unusual access times, repeated failed attempts, or credentials used at multiple locations simultaneously all warrant investigation. Audit trail capabilities provide this visibility but only deliver value when someone regularly reviews the data. Designate responsibility for log monitoring and establish clear escalation procedures for suspicious activity.
Integration with CCTV creates powerful verification capabilities. When access control logs show someone entered at 2am, corresponding video footage confirms identity and activities. This layered approach deters misconduct since users know their actions face multiple verification methods. Burglar alarm systems should coordinate with access control to prevent false alarms when authorised users enter outside normal hours.
Routine maintenance preserves system integrity and prevents failures that compromise security. Software updates patch vulnerabilities and add features that enhance protection. Hardware inspections identify worn card readers, failing locks, or backup batteries needing replacement before they cause access disruptions. Schedule these tasks quarterly rather than waiting for component failures.
Access control maintenance best practices:
- Update controller firmware and management software within one month of releases
- Test backup power systems monthly to ensure doors secure properly during outages
- Inspect card readers and biometric sensors quarterly for physical damage or wear
- Review all active credentials quarterly and deactivate unused accounts immediately
- Conduct annual security audits examining permissions, logs, and physical components
- Document all maintenance activities and system changes for compliance and troubleshooting
- Establish incident response plans specifying actions for various security events
- Train new administrators thoroughly and provide refresher training annually
Staff training ensures people understand both technical operation and security protocols. Administrators need comprehensive knowledge of granting permissions, running reports, and responding to alerts. Regular users should know proper credential handling, reporting lost cards, and recognising security concerns. Clear protocols prevent inconsistent access decisions that create vulnerabilities.
Cloud-based monitoring enables remote oversight particularly valuable for multi-site property managers. You receive instant alerts about security events and can adjust permissions without visiting properties. However, cloud connectivity requires robust cybersecurity including strong passwords, multi-factor authentication for administrative access, and regular security assessments. Balance convenience against potential cyber risks based on your threat profile.
Explore analytic CCTV capabilities that complement access control through intelligent monitoring. The installation guide covers integration approaches for comprehensive security systems.
Enhance your property security with expert access control services
Implementing effective access control requires specialist knowledge of technologies, regulations, and installation best practices. Professional security providers design systems tailored to your specific property requirements whilst ensuring compliance with relevant standards.
Expert installers assess your premises comprehensively, identifying vulnerable entry points and recommending appropriate solutions. They configure door access control systems to match your operational needs whilst maintaining security integrity. Professional installation ensures proper integration with existing infrastructure including CCTV, alarms, and building management systems.
Ongoing support maintains system performance through regular maintenance, software updates, and rapid response when issues arise. Trusted local providers understand Essex and London property requirements, offering responsive service that minimises security disruptions. Combining access control with comprehensive solutions like CCTV installation and burglar alarms creates layered defence that significantly reduces security risks whilst improving overall property safety.
Frequently asked questions
What is the most secure access control method for commercial properties?
Biometric systems provide the highest physical security since biological credentials cannot be shared or stolen like cards. However, combining biometrics with RBAC or ABAC methodologies delivers optimal protection by adding granular permission management to strong authentication. Consider your specific threats and budget when selecting systems, as layered approaches using multiple verification methods often outperform single high-security solutions. Review door access control options to compare security levels.
How do cloud-based access control systems compare to on-premise ones?
Cloud systems enable remote management from any internet connection, making them ideal for multi-site operations or managers requiring flexible administration. They scale easily and reduce on-site IT requirements. On-premise controllers provide direct control and operate independently of internet connectivity, eliminating cyber risks from cloud exposure but limiting remote access capabilities. Choose based on your operational needs, IT resources, and security priorities as outlined in the installation guide.
What maintenance is required for electronic access control systems?
Regular software updates patch security vulnerabilities and add functionality, typically needed quarterly. Hardware inspections identify worn components before failures occur, whilst backup power testing ensures doors secure properly during outages. Quarterly access permission reviews prevent outdated credentials from creating security gaps. Professional maintenance contracts ensure these critical tasks occur consistently. Learn about seamless integration and maintenance approaches for sustained system performance.
Can access control systems integrate with existing security infrastructure?
Modern access control integrates readily with CCTV, burglar alarms, and building management systems through standard protocols. Integration creates layered security where access events trigger camera recording, unusual patterns generate alerts, and alarm systems coordinate with authorised entry. Professional installers assess your current infrastructure and design integration solutions that maximise existing investments whilst enhancing overall protection. Proper integration significantly improves incident response and security effectiveness compared to standalone systems.
How quickly can access permissions be changed in electronic systems?
Electronic systems enable instant permission changes through management software. Deactivating a lost card or adding a new employee takes seconds compared to days or weeks for rekeying traditional locks. Cloud-based systems allow remote changes from any location, whilst on-premise controllers require local network access. This flexibility proves invaluable during security incidents or staffing changes, making electronic access control far more responsive than mechanical alternatives for dynamic business environments.